Simmer there turbo.
"Microsoft Windows SMB Shares Unprivileged Access".
http://nessus.org/plugins/index.php?view...e&id=42411
It means that it's Guest Readable, this is the "fix"
"To restrict access under Windows, open Explorer, do a right click on
each share, go to the 'sharing' tab, and click on 'permissions'."
Ok. Who cares about who signed the SSL stuff? It still means your bits aren't plain text over the network. Which is the point. I run self generated SSL on almost everything I can. Stuff is encrypted between here and there.
SMB Guest Account Local User Access
http://www.nessus.org/plugins/index.php?...e&id=26919
So.... you can access it as a guest as any user. Again. If this is a network server, you should be able to do this on shared shares.
OpenSSL Detection - Yeah. It detected OpenSSL. Literally, that's the "Bug".
http://www.nessus.org/plugins/index.php?...e&id=50845
mDNS Detection - It is running mDNS. You can find out about the machine. (Meaning XBMC, which advertises stuff over mDNS is "equally" as vulnerable).
"The remote service understands the Bonjour (also known as ZeroConf or
mDNS) protocol, which allows anyone to uncover information from the
remote host such as its operating system type and exact version, its
hostname, and the list of services it is running."
Synopsis : The manufacturer can be deduced from the Ethernet OUI.
Description : Each ethernet MAC address starts with a 24-bit 'Organizationally
Unique Identifier'.
These OUI are registered by IEEE.
How would you propose the web admin work without... web. browsable. directories.. OMG. GOOGLE HAS WEB BROWSABLE DIRECTORIES TOO. THEY"VE BEEN ROOTED.
http://www.nessus.org/plugins/index.php?...e&id=40984 (It means you can use a web browser).
The remote host listens on UDP port 137 or TCP port 445 and replies to
NetBIOS nbtscan or SMB requests.
Note that this plugin gathers information to be used in other plugins
but does not itself generate a report.
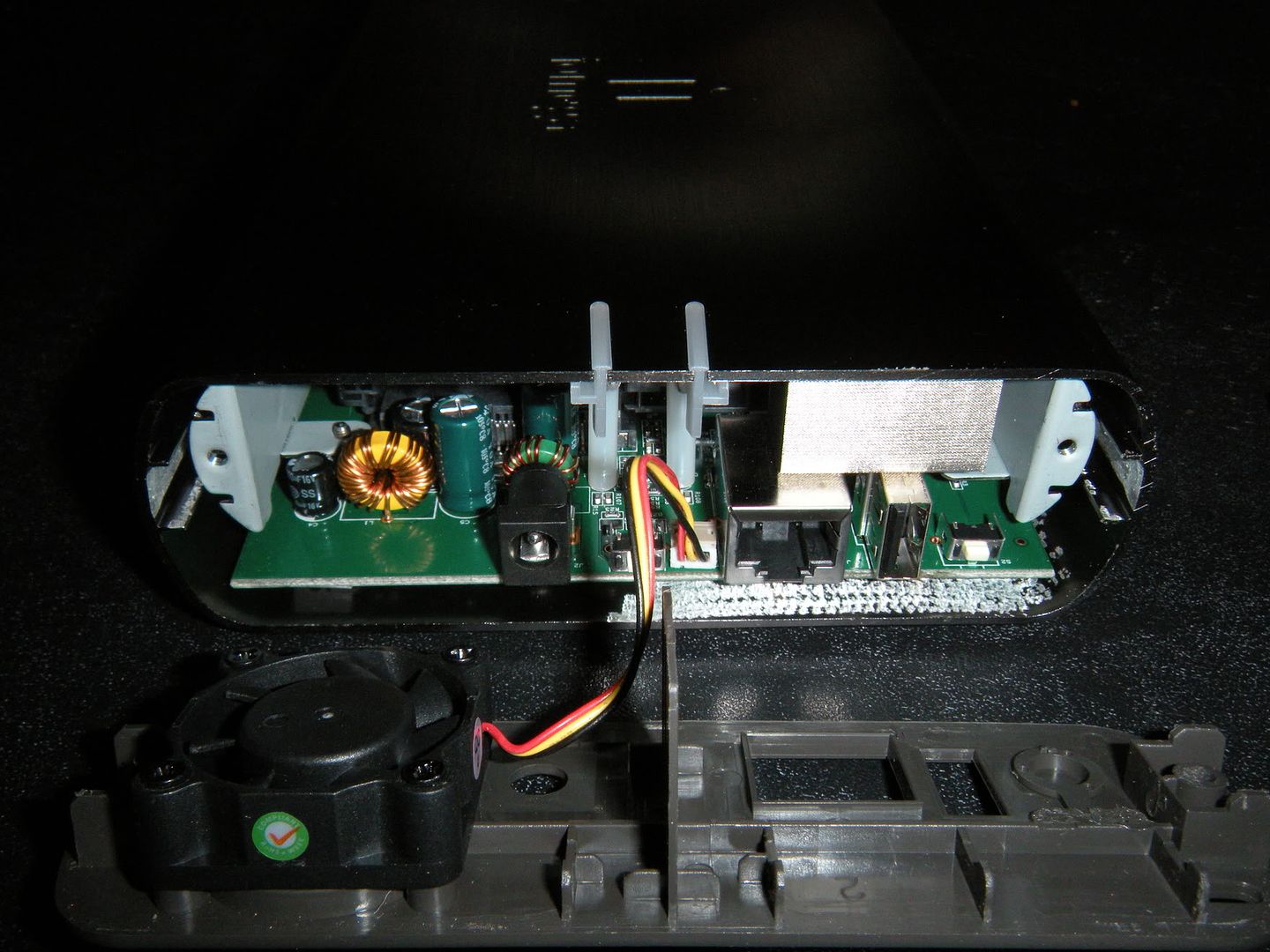
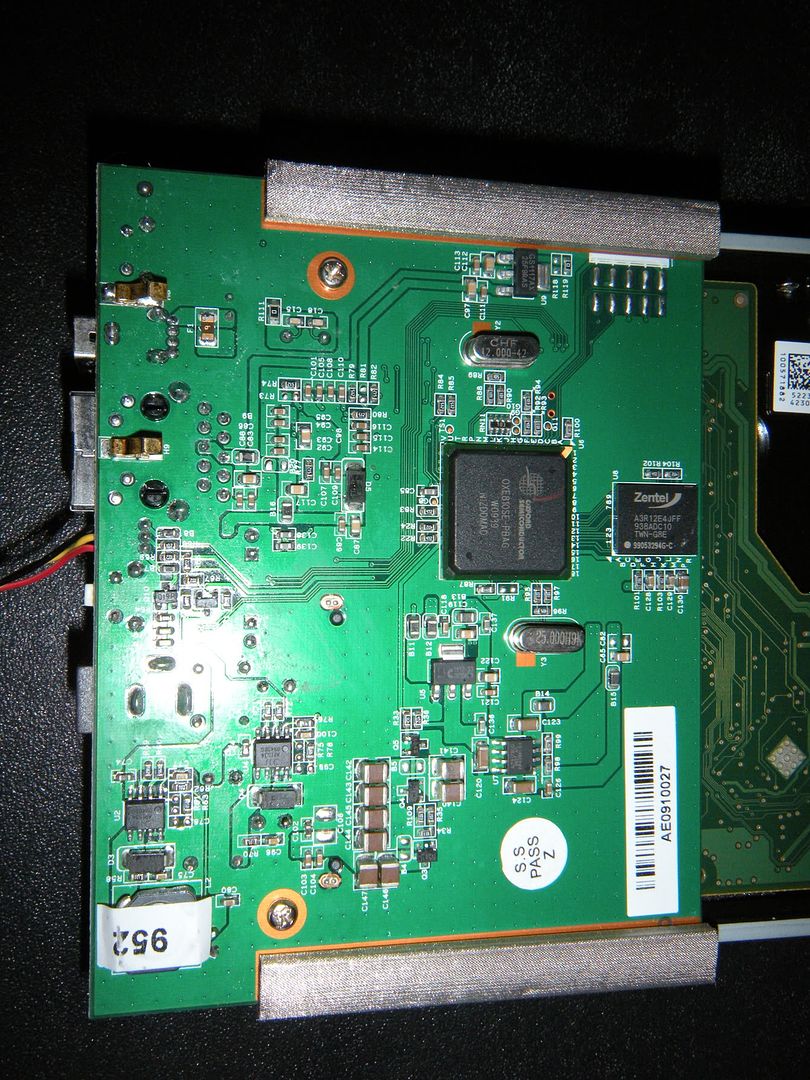
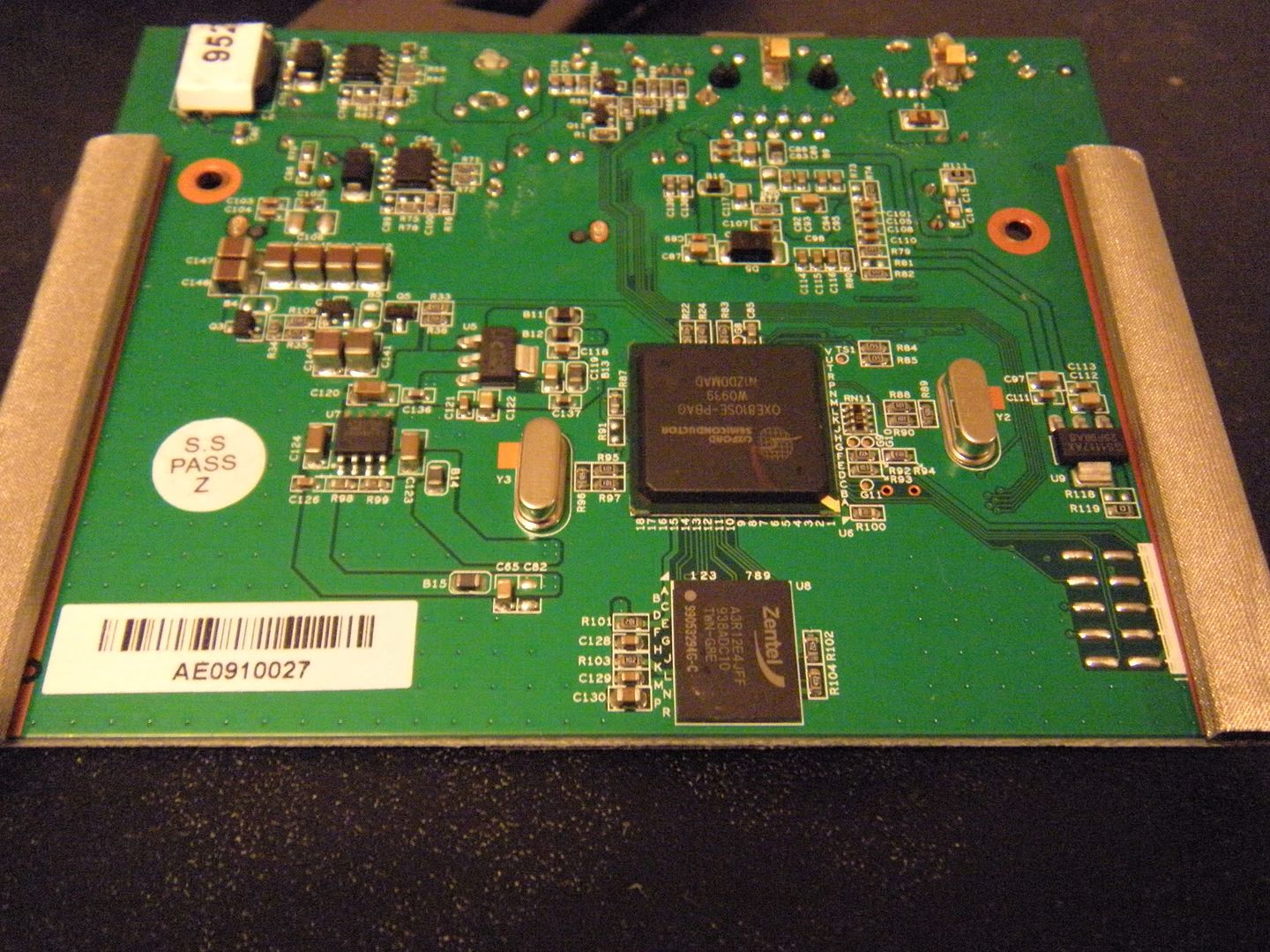
Sounds pretty much like a NAS box.
Have you tried scanning your XBMC box? I'd be interested in how many it comes back with. Like those really horrible day 0-exploits that Russian crackers use like "Ping" and "Can figure out Ethernet Card OEM"